It’s a message that no one wants to receive: your corporate video containing sensitive information was somehow shared outside of your company, and could potentially cause a PR nightmare. The question is, what do you do now?
Make Sure You’re the First to Know
If the video contains highly confidential information, set up Google Alerts (or a similar notification service) for either the subject of the video, its title, or keywords that might be used to describe it. This way, if a search engine locates the video somewhere on the web, you’re more likely to know about it sooner rather than later. Try to be specific and use long-tail phrases, or you might wind up with a lot of false positives.
You can also pick a video hosting provider that offers detailed reporting on where your videos are being played, and can track individual viewers at a very granular level. If you notice a strange location or IP address in your reporting, for instance, you’ll want to investigate right away.
Take Stock
If it appears that someone did misappropriate your video, first and foremost, don’t panic, but get to work quickly. Gather as much information as possible about Who, What, Where and When in order to ensure your subsequent actions are thorough and effective.
Quickly track down all the locations where the video is being shared without permission as best you are able. The goal is to take it down as quickly as possible before it has a chance to really spread.
To do so, start at the top. Try to identify the video hosting provider where the video has been uploaded. If the player doesn’t feature their logo, you can still find out by right-clicking on the page, selecting Inspect (or Inspect Element depending on your browser), and locating the video embed code on the page. Usually it’s contained in an iFrame or div element, and the hosting provider’s name will be evident.
Make careful note of the platforms where you’ve been able to locate the video, as well as any usernames associated with the unwanted uploads.
Get Ahead of It
Contact all key stakeholders who might be affected by this event to make sure they are aware of the situation, and that you’re doing all you can to contain it.
Remaining factual and transparent will help engender trust that everything will soon be under control. Issue periodic updates when you gain new information so no one is left wondering what’s happening.
Issue Takedown Notices
Reach out to the platforms where you have located the video in question and contact their support team to issue a takedown notice. Be prepared with proof of ownership of the video, a way of verifying your identity, and the usernames you were able to pinpoint that may have shared your video without permission.
Video hosting platforms are usually quick to act on this type of complaint, and are better able to quickly take action against multiple accounts at a time than if you were to try to contact each person sharing your video individually.
Counteract the Damage
This type of unfortunate event can have ramifications beyond short-term embarrassment. Depending on what the video contained, you could face issues with business partners, investors, or employees for starters.
If necessary, first check with a legal advisor, then consider how you can best remedy the damage caused by the leak of your video. Sometimes, addressing it publicly, via Twitter, a blog post, or a press release, makes sense because it takes the shame out of the situation. This works because you can gain control of the dialogue by taking ownership of the situation.
If the video was not shared widely, however, that might not be your wisest approach as far as how to publicly handle the situation. Tweeting or blogging about it might create a mountain out of a molehill, or motivate people to try to find the video in question. Start by communicating clearly and reassuringly with any impacted stakeholders, and then re-evaluate if a broader approach is needed.
The third option is a tad riskier – don’t address it publicly at all. Handle everything quietly and discreetly, and hope no one notices. Given the short lifespan of most content online, you might just get away with it. This, of course, could allow the conversation to run away from you, or could give the erroneous impression that you don’t really care in the event word gets out.
No matter which approach you take, rather than playing a blame game, it’s important to be forthright with the information available to you, and to assure others that controls have been put in place to prevent subsequent information leaks.
An Ounce of Prevention
Speaking of preventative controls, avoiding this situation entirely is clearly the best course of action. Luckily, with internal video communications, there are many good options for ensuring your video can’t be shared beyond your company walls, by non-employees, or anyone without permission to view it.
Starting with the simplest option, allowed domains is a video security setting available to all SproutVideo accountholders that allows you to specify the websites on which your videos can play. Anywhere else, they simply won’t load on the page and will display an error message instead. This prevents people from grabbing your video embed code from the page source information, and placing it on another website. This won’t, however, prevent sharing of the URL of the page on which your video is embedded.
A slightly more sophisticated but similar option is signed embed codes. Signed embed codes require some programming knowledge to implement, but make it so that the video embed code requires a secret signing key in order to load. This means that your video embed code will only load in certain circumstances under your control, and can’t be shared on other websites.
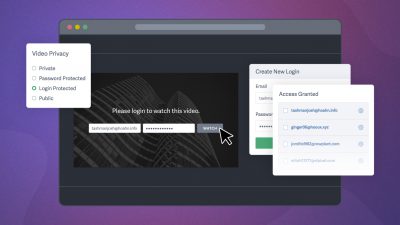
To limit the sharing of the video no matter where it is located, you can use login protection for your videos, and restrict the period of time or number of logins for which a given viewer can access your videos. This would allow your selected viewers to view your video, but would limit the extent to which your video could be shared without permission.
Another simple yet effective option is to implement IP address restriction for your videos. This means only viewers on approved network connections can view your videos. This is an excellent option for companies that own blocks of IP addresses, or use a VPN, so that all employees are on the same network. IP address restriction only works in instances where you already know, or can easily find out, the IP address of all your intended viewers. For anyone outside of your designated networks, your videos won’t load.
Finally, using single-sign-on (SSO) in conjunction with a SproutVideo website makes it so that only people with company-issued credentials can access your videos. Although it requires a little extra effort to setup initially, SSO is very low maintenance going forward. SSO works by redirecting to your company’s Identity Provider to authenticate viewers when they try to log into your video website to view your videos. If they aren’t registered in your company’s database, they won’t be able to access any content.
In summary, controlling access to your videos in the first place is the best way to ensure they won’t be shared without your permission. If you do wind up facing a potential disaster, remember to breathe, and use these tips to mitigate the damage.
Here’s hoping you never need any of that advice! Let us know if you have any questions in the comments below.