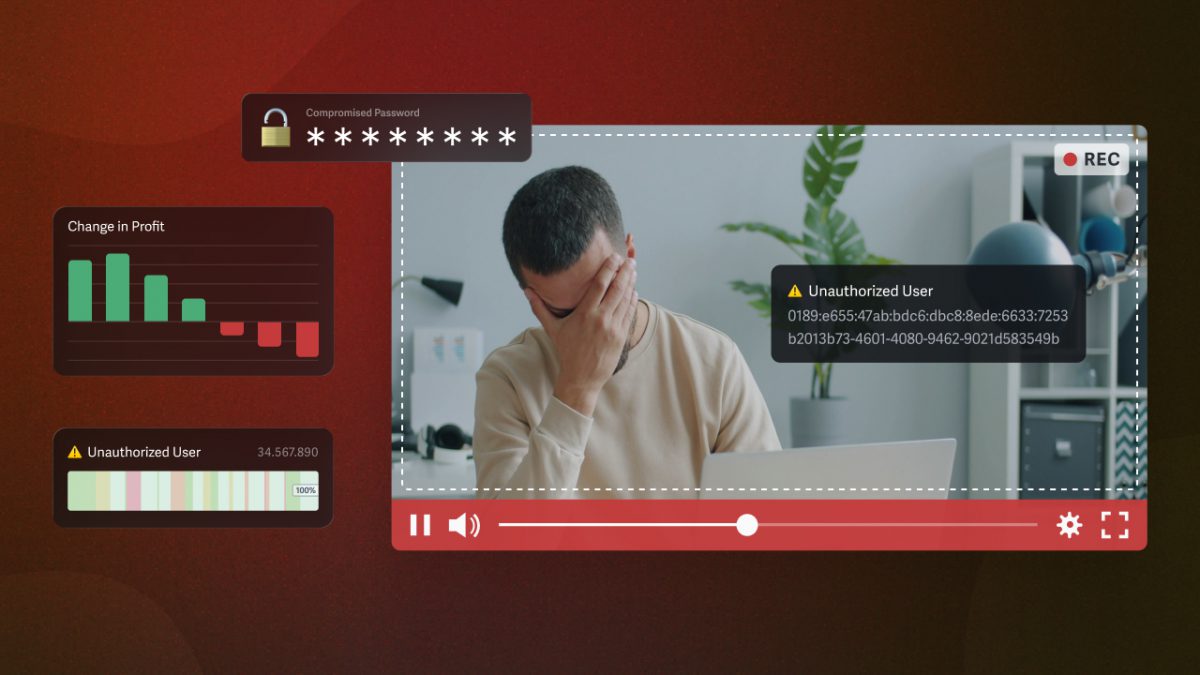
It starts with one unintended viewer. A confidential product demo with unreleased features shows up in a reporter’s inbox. Your investor update with Q4 projections and an 18-month roadmap gets forwarded to someone who was never supposed to see it. An internal compliance training video with sensitive HR guidance falls into a competitor’s hands.
These scenarios aren’t hypothetical edge cases reserved for large enterprises. They happen to businesses of every size, and the consequences reach far beyond the moment of discovery.
In a tighter economic environment, the costs of a video leak are even harder to absorb. Margins are thinner, legal and compliance budgets are under pressure, and every disruption, whether financial, operational, or reputational, lands with greater relative force.
The instinct for most businesses is to focus on whether a leak might happen, rather than what it would actually cost if it did. But you don’t need to be an enterprise with a dedicated security team to protect your business content. Get ahead of potential security breaches and treat secure video sharing as the business safeguard it truly is.
In this guide, we break down:
- The true cost of video leaks to businesses
- Why leak costs hit harder in today’s environment
- What a practical, secure video strategy looks like
Gain a clear picture of what’s at stake and a strategy for protecting your video assets.
Table of Contents
- How Business Videos Leak in the First Place
- The Direct Financial Costs of Video Leaks
- The Reputational Costs of Video Leaks
- The Operational Costs of Video Leaks
- Why Leak Costs Hit Harder During an Economic Downturn
- What a Video Leak Prevention Strategy Looks Like
- The Cost of Prevention vs. The Cost of Video Leak
How Business Videos Leak in the First Place
Most people imagine a video leak as the result of a deliberate, sophisticated attack. In reality, the most common causes are mundane, which makes them easy to overlook.

None of the following security breaches requires a technical background or bad intent; still, the:
- Link is forwarded to someone outside the intended audience
- Password is shared across a team and then shared again
- Video is downloaded to a personal device that later gets compromised
- Screen recording is made during a virtual meeting
Human error is responsible for 74% of all cyber incidents, but the way content gets shared is the main vulnerability and determines how videos can leak.
Quick, Frictionless Sharing
When you share a video using a generic link — the kind that can be copied, pasted, and forwarded without friction — you have effectively handed that content to everyone who touches that link. There is no way to know who has seen it, revoke access after the fact, or prevent the next person in the chain from passing it along.
Public and Insecure Platforms
Platforms built for consumer video sharing, like YouTube (even when set to private) or Google Drive, were designed for ease of sharing and accessibility, not for protecting against video leaks. Using these platforms for confidential business content is a structural mismatch, regardless of how carefully the sender intends to protect the video.
Insecure Sharing Workflow
When it’s acknowledged that the method of video sharing determines the level of vulnerability to content, the conversation can shift from blaming an individual to adjusting the company process.
A client success manager who forwards a video link to the wrong contact did not make an unusual or careless mistake; they used the tool they had available. An L&D manager who shares a training video via a downloadable link because that was the fastest option is not failing in their security responsibilities. The failure is in the system, not the person.
Understanding that most video leaks happen through ordinary, low-friction sharing behaviors is the starting point for building a sharing workflow that actually protects your content. For a closer look at the most effective methods for secure video sharing, visit our complete guide to protecting business videos.
The Direct Financial Costs of Video Leaks to Businesses
Of all the ways a video leak affects a business, the financial damage is the most immediately legible, and it rarely stops at just one line item.
Product Releases & Marketing Campaigns
For those sharing pre-release product content or unreleased marketing campaigns, the most direct financial cost is lost revenue via:
- A product launch video that surfaces before the embargo window closes eliminates the competitive advantage the launch was designed to create.
- Campaign assets that leak prematurely, rendering the campaign less effective, forcing costly rework, a revised rollout timeline, and expenses that were not budgeted for
In highly competitive industries where the timing of a product reveal drives significant customer acquisition, the revenue impact of a premature disclosure can reach well into the hundreds of thousands of dollars.
Legal Fees & Client Data
Legal fees and settlements represent another category of direct financial cost, and they can be substantial. If a leaked video is shared in violation of a non-disclosure agreement or its contents violate the terms of a client contract, the company can face immediate legal exposure.
Regulated Industries with Personal Data
If a leaked video contains protected personal data, such as employee Personally Identifiable Information (PII), client information, or health-related content, the regulatory exposure can significantly compound the financial damage.
GDPR
If a leaked video contained protected personal data, including employee PII, client information, or health-related content, the regulatory exposure compounds the financial damage significantly. GDPR applies to any organization that processes the personal data of EU residents, regardless of where the business itself is located. Any of the following can bring a business within scope:
- A training video that captures an employee’s name and image
- A recorded client presentation that includes identifiable contact details
- An investor update that references personal financial information
Under GDPR, organizations can face fines of up to €20 million or 4% of their global annual turnover for more severe violations involving unauthorized data disclosure. The key principle is that the business is responsible for implementing appropriate technical and organizational measures to protect personal data, and a video shared through an insecure channel without adequate access controls is unlikely to satisfy that standard. In 2024 alone, European data protection authorities issued an aggregate total of €1.2 billion in GDPR fines.
For businesses operating across borders, GDPR exposure is not a hypothetical risk: it is a standing liability that a single insecure video share can activate.
HIPAA
For healthcare organizations, HIPAA applies to any covered entity or business associate that handles protected health information, and video content is explicitly within scope. A training video that captures a patient’s name or face, a recorded clinical workflow showing identifiable patient data, or a telehealth session recording stored on behalf of a clinic all constitute PHI under HIPAA. For L&D teams in healthcare settings, every training video and clinical demonstration is a potential compliance liability if it reaches an unintended audience.
The financial consequences are tiered by severity. Accidental disclosure of PHI on video recordings can lead to fines ranging from $127 per violation to $63,973, with cases involving willful neglect carrying individual settlements into the millions. In 2024 alone, OCR issued $18.4 million in HIPAA settlements, with 86% of violations attributed to failures organizations could have prevented. Post-breach response activities constitute roughly 30% of total breach costs with an average of $1.32 million, and these costs often extend 12 to 18 months beyond the initial incident.
SOC 2
SOC 2 is a voluntary auditing framework developed by the American Institute of Certified Public Accountants (AICPA) that evaluates an organization’s security controls across five Trust Services Criteria, with security as the only mandatory criterion.
While it carries no statutory fines, its consequences for B2B businesses that handle customer data are commercial and immediate. When a confidential video leak exposes gaps in access controls, insufficient audit logging, or inadequate viewer-level permissions, it surfaces exactly the kind of control failures that enterprise customers and procurement teams use to disqualify vendors. The business cost does not require a regulator to get involved: a third of organizations have lost deals specifically due to lacking required security certifications like SOC 2.
For SaaS companies, marketing technology vendors, and any business selling into enterprise accounts, a video leak that calls your access control practices into question can stall or kill sales cycles that were already in progress. Demand for SOC 2 engagements rose nearly 50% in 2023 according to an AICPA survey, and 72% of organizations that pursued an audit did so specifically to win business. When a prospective enterprise customer asks for evidence of your security controls and the answer is complicated by a recent incident, the deal often moves to a competitor who can provide a quick, clean answer.
The Bottomline
The financial stakes are well-documented: Data breach costs hit a record high in 2024, with the global average reaching $4.88 million — up 10% from the prior year. While that figure encompasses all types of data incidents, it reflects the full weight of legal, regulatory, and remediation costs that cascade from a single security failure. For smaller businesses, even a fraction of that figure represents a devastating financial blow.
The Reputational Costs of Video Leaks
The reputational consequences of a video leak are harder to bound than legal fees, but they tend to last far longer.
Client Relationships
When a confidential client deliverable, such as a custom product demo, a strategic presentation, or a sensitive training video, surfaces outside the intended audience, the client relationship is immediately placed under strain.
Clients entrust vendors with access to their business context, their strategic priorities, and sometimes their own sensitive data. A leak signals that the trust placed in your organization was not honored with the proper protection. In fact, 65% of data breach victims report a loss of trust in an organization following a security incident, creating lasting consequences for customer loyalty and retention. In a client services business, that erosion of trust is often irreversible.
Investor Trust
For companies sharing financial or strategic content with investors, the consequences of a leak are particularly acute. A single leaked investor update that reveals unreleased projections, mergers and acquisitions (M&A) discussions, or strategic pivots can create serious legal exposure under securities regulations, disrupt deal timelines, and signal to investors that the organization lacks the controls they expect.
Once shaken, investor confidence is difficult to rebuild quickly. The largest and most salient data breaches are associated with a 5-to-9% decline in intangible reputational capital. For a company in the middle of a fundraising or strategic transaction, even a modest decline in investor confidence can carry outsized financial consequences.
Brand Damage
Brand damage from leaked marketing and product content comes with its own cost and often occurs before a company has the chance to intercept it. A product video, for example, that surfaces before launch removes the element of surprise, giving competitors an early look at positioning and features, and forces your marketing team to create new messaging on the fly.
Employee Morale
There’s also an internal dimension to reputational damage that is equally real but less often discussed. In the wake of a video leak or breach, employee morale and productivity can suffer as staff grapple with feelings of guilt, frustration, and anxiety. A team that has lived through a leak, and the scrutiny, blame, and remediation work that follows, is harder to retain and slower to rebuild.
The Bottomline
Among businesses that experience a data breach:
- 47% struggled to attract new customers afterward
- 43% lost existing customers
- 38% experienced damaging media publicity
Reputational damage is harder to quantify than a legal settlement, but it is often the most lasting consequence of a video leak.
The Operational Costs of Video Leaks
The operational disruption that follows a video leak is rarely accounted for in advance, but it consumes enormous amounts of organizational time and energy.
Investigation
The moment a leak is discovered, an investigation begins: which video leaked, through which channel, to whom, and when. For organizations without an audit trail (detailed viewer-level records of who accessed a video and when), this investigation can consume weeks of time from IT, legal, and leadership.
Detection and escalation now represent the most expensive phase of a data breach response, averaging $1.47 million for the forensic investigation and specialist consultation required during critical early containment. Even at a fraction of that scale, the investigation resources consumed by a video leak represent a high operational cost.
Containment
Rebuilding or revoking access across a compromised sharing workflow is time-consuming and often technically complex. If a video is shared via a generic link, there is no way to revoke access for parties who should not have it. The entire workflow must be rebuilt..
Furthermore, if the video was copied before the breach was discovered, revoking access does nothing for versions already in circulation if there’s no way to trace the leak source.
The window between when a breach occurs and when it is detected is critical; organizations that contain a breach within 30 days save an average of $1.12 million compared to those with longer containment periods. For video content without access controls via user authentication and protections from piracy, that window often cannot be closed at all.
Leadership Timesink
Leadership distraction is a real cost that’s rarely measured. When a video leak occurs, it pulls founders, executives, legal counsel, and communications teams away from revenue-generating work. High-level strategy sessions with executive team members following a security incident, typically involving the CEO, CFO, legal, and communications leads, can cost between $3,000 and $5,000 per meeting, with multiple meetings required over the course of a response.
For small and mid-size businesses without large functional teams, the opportunity cost of a single video leak can consume weeks of leadership bandwidth. And, if content needs to be recreated or re-released in the form of a new product demo, a revised investor presentation, a replacement training module, the production cost is added on top of all the other operational expenses the leak has already generated.
Why Leak Costs Hit Harder During an Economic Downturn
In an environment where every budget dollar is scrutinized and every operational disruption carries greater relative weight, a video leak is simply more expensive to absorb. Thinner margins mean that a legal settlement or a regulatory fine that would have been manageable in a stronger revenue environment can now represent a material portion of operating cash.
Business Health
Costs from lost business and post-breach response rose nearly 11% over the previous year, even as organizations worked to improve their detection capabilities. When revenue is under pressure and operating expenses are already being cut, absorbing a six- or seven-figure breach-related expense becomes a genuine threat to a business’s health.
Legal and compliance budgets are also under pressure in a downturn, which shifts the calculus sharply in favor of prevention. The cost of responding to a video leak can include forensic investigation, legal counsel, regulatory filings, and crisis communications. And these costs do not shrink or wait when a company’s budget is tight.
Trust Erosion
Buyers and investors are also more risk-averse during an economic downturn, which amplifies the reputational consequences of a leak. In a strong market, a client might absorb a security incident, accept a vendor’s remediation plan, and move forward.
In a tighter environment, the same incident becomes grounds for a contract review, a delayed renewal, or a decision to consolidate vendors and reduce risk. After a security incident, 70% of consumers said they would stop doing business with a company, with more than half (58%) believing a brand is not trustworthy if it experiences a breach. For B2B businesses that rely on long-term client relationships, this level of trust erosion is particularly damaging when clients are already looking for reasons to cut costs or reduce vendor exposure.
The Bottomline
For every dollar invested in data breach prevention measures, organizations save three dollars in potential leak costs. That means prevention isn’t just cheaper than response — it’s the only option that doesn’t risk serious operational harm.
Lean teams simply do not have the capacity to manage a full breach response effectively while simultaneously running the business, which means that a video leak during a tight period can create a cascading series of disruptions that takes months to resolve.
What a Video Leak Prevention Strategy Looks Like
The foundation of any effective video leak prevention strategy is simple in principle: the sharing method should match the sensitivity of the content.
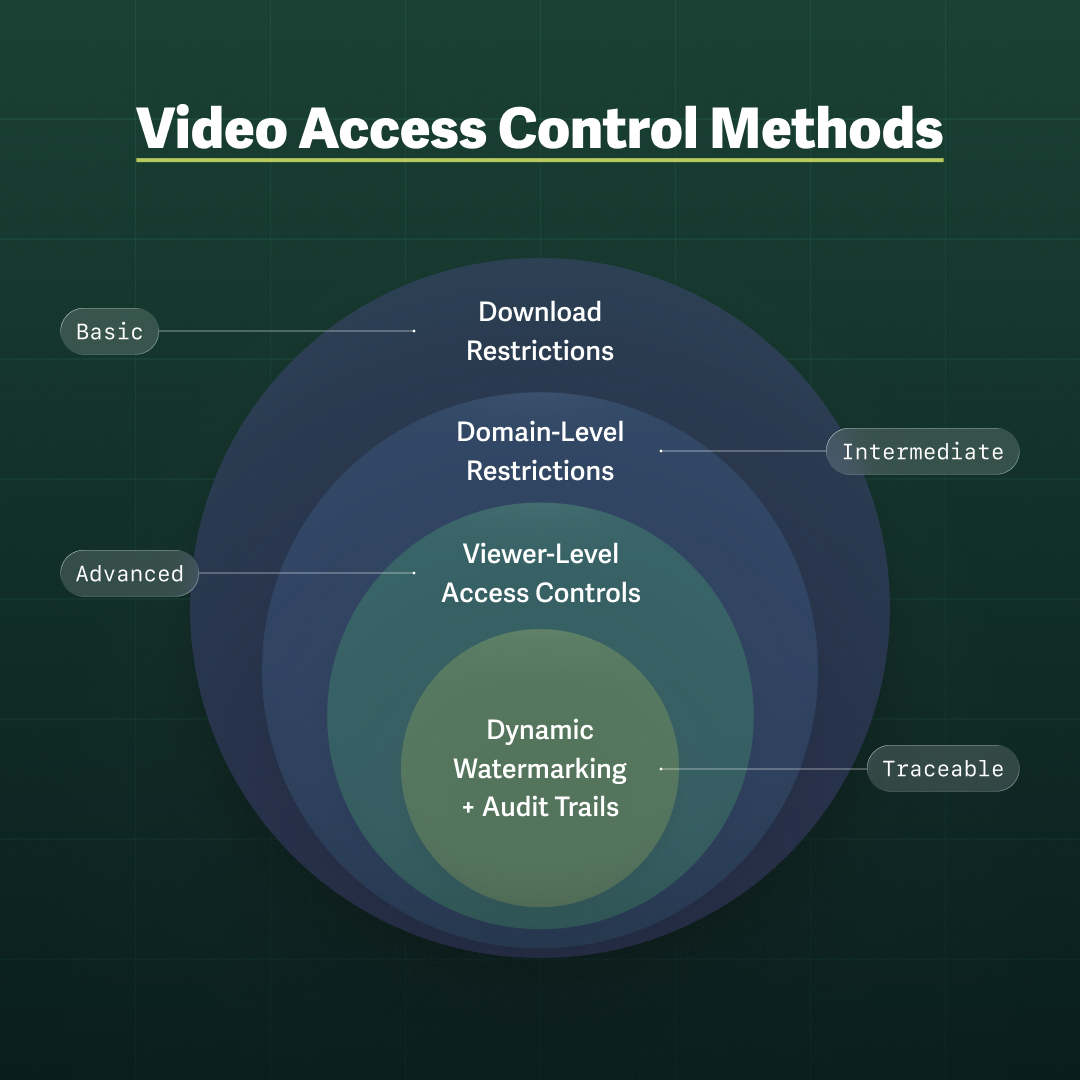
Not every video requires the same level of protection. A publicly available brand video has different requirements than a confidential investor update, and an internal training module for a general audience has different requirements than a compliance training that contains sensitive HR guidance. Step one is categorizing your video content by sensitivity level and assigning an appropriate sharing method to each category.
High Sensitivity Content
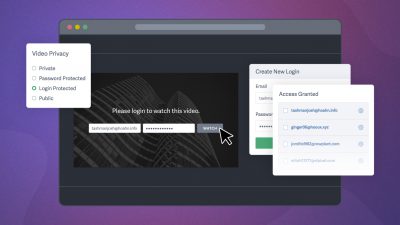
For high-sensitivity content, several controls work together to close the most common leak vectors.
Login Protection or SSO
Login protection and SSO require viewers to authenticate before accessing content, meaning a forwarded link is worthless, and viewers can be held accountable.
This form of viewer-level access control assigns specific permissions to individual users, so a video shared with five people cannot be accessed by an unintended sixth person without explicit credential sharing, which can be spotted by reviewing engagement data.
Dynamic Watermarks
Dynamic watermarking is one of the most effective deterrents for the unauthorized use of confidential video content. Visible dynamic watermarks display viewer-identifying information, typically the viewer’s name, email address, and IP address, in the video file. Additionally, invisible dynamic watermarks ensure that even if a viewer screen-records the content, the recording carries an embedded, traceable watermark that can be used to identify the source of the leak. Learn more about how dynamic watermarking works and why it is one of the most effective tools for protecting business video content.
Engagement Metrics
Maintaining an audit trail of who watched what and when gives your team the information it needs to investigate a leak quickly, contain the damage, and take appropriate action. A complete viewer analytics record removes the ambiguity that makes leak investigations so time-consuming and expensive.
The Cost of Prevention vs. The Cost of Video Leak
A video leak creates consequences that ripple through a business for months or years, some measurable, some harder to quantify but no less real:
- Direct costs: legal fees, regulatory fines, forensic investigation, and crisis communications are substantial and arrive immediately
- Reputational costs: lost client trust, damaged investor confidence, brand disruption, and reduced employee morale are often longer lasting than the financial hit
- Operational costs: leadership distraction, workflow rebuilding, and content recreation arrive on top of everything else, at a moment when your team has the least capacity to absorb them
The business case for secure video hosting comes down to a straightforward comparison: what does it cost to prevent a leak versus respond to one? Even if your immediate exposure is a fraction of the $4.88 million global average, it will almost certainly exceed the annual cost of a professional secure video hosting platform.
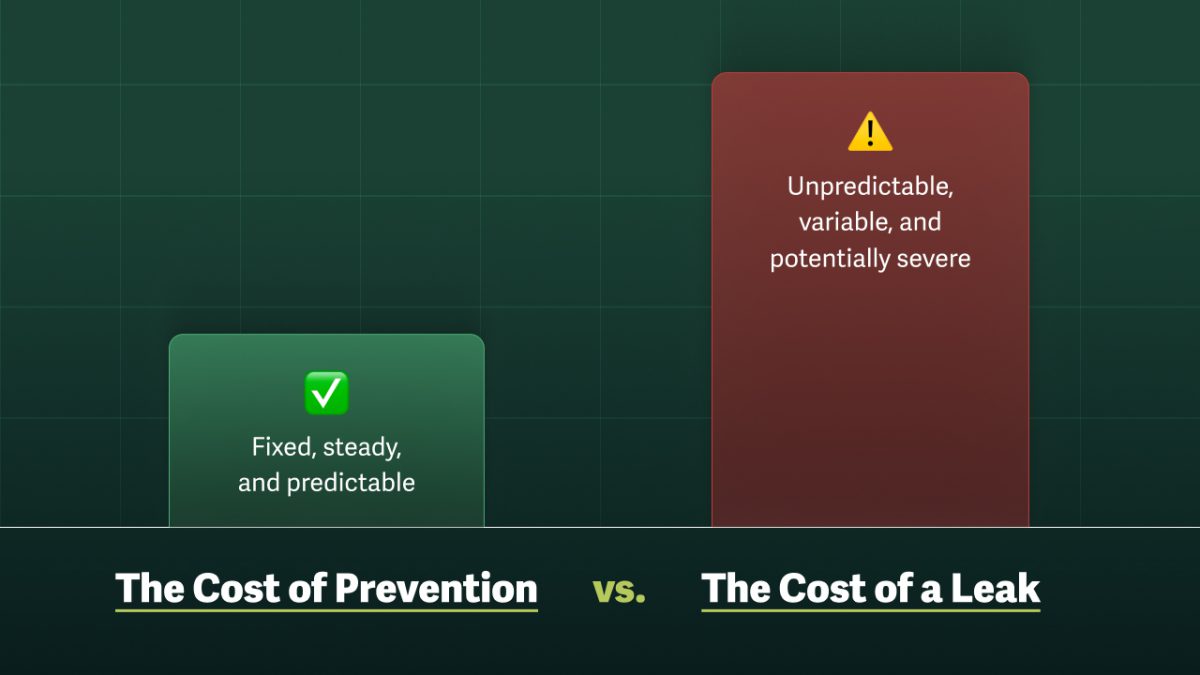
The question is not whether your IT team can implement access controls. The question is whether your business can afford the consequences of a leak, and whether the people responsible for confidential content have the tools they need to share it securely. Waiting until a leak occurs to build that workflow is the most expensive strategy a business can pursue.
If your current video sharing workflow relies on generic links, consumer platforms, or tools without access controls, now is the time to audit it. Start a free trial with SproutVideo and see how easy it is to bring enterprise-grade video security to every type of content you share, from client deliverables and investor updates to internal training and pre-release campaigns.
Your video content is valuable. Protect it like it is.