Restricting video access allows businesses to control exactly who can watch a video, where they can view it, and how they can access it.
From employee training and internal communications to client collaboration and monetized content, private video sharing is core to business operations.
In these situations, video access controls ensure business videos are shared securely and intentionally, with only authorized viewers.
Determine the video access restrictions your business needs. Explore seven ways businesses protect video for secure, private sharing.
What Does It Mean to Restrict Video Access?
Restricting video access in a business means controlling who can watch a video and where they can watch it. Video access controls limit playback to:
- Employees, Clients, or Customers
- Company Website or Internal Portal
- A Set Period of Time
- An Office or Other Work Environment
- Specific World Regions or Countries
A secure video hosting platform, such as SproutVideo, keeps your source video file protected and private by default, preventing direct downloads and search indexing.
When it’s time to share that video privately, access restrictions are the first line of defense to protect your content.
Note: This article does not cover how to prevent video theft and unauthorized redistribution—watch our two-minute guide to secure video sharing.
Common Business Use Cases for Private Video Sharing
These business use cases often require restricting video access. You can click each recommended access control to jump to that section for more information.
| Business Use Case | Recommended Access Controls |
| Training, Onboarding & Compliance | SSO, Login Protection, IP Restrictions |
| Internal & Leadership Communications | Unlisted Video Link, Login Protection, IP Restrictions |
| Secure Client Collaboration | Unlisted Video Link, Password, Login Protection |
| Monetized or Restricted Video Content | Login Protection, Gated Access, Geo-Whitelisting |
In addition to the controls above, businesses can also implement role-based permissions for the video hosting account to limit and track team member actions.
Learn More: 7 Reasons Businesses Use Private Video Hosting Platforms vs YouTube
7 Ways to Restrict Video Access for Private Sharing
Most businesses layer multiple access controls for private video sharing. Use this list to evaluate which access controls best fit your audience, distribution needs, and use case.
1. Share An Unlisted Video Link
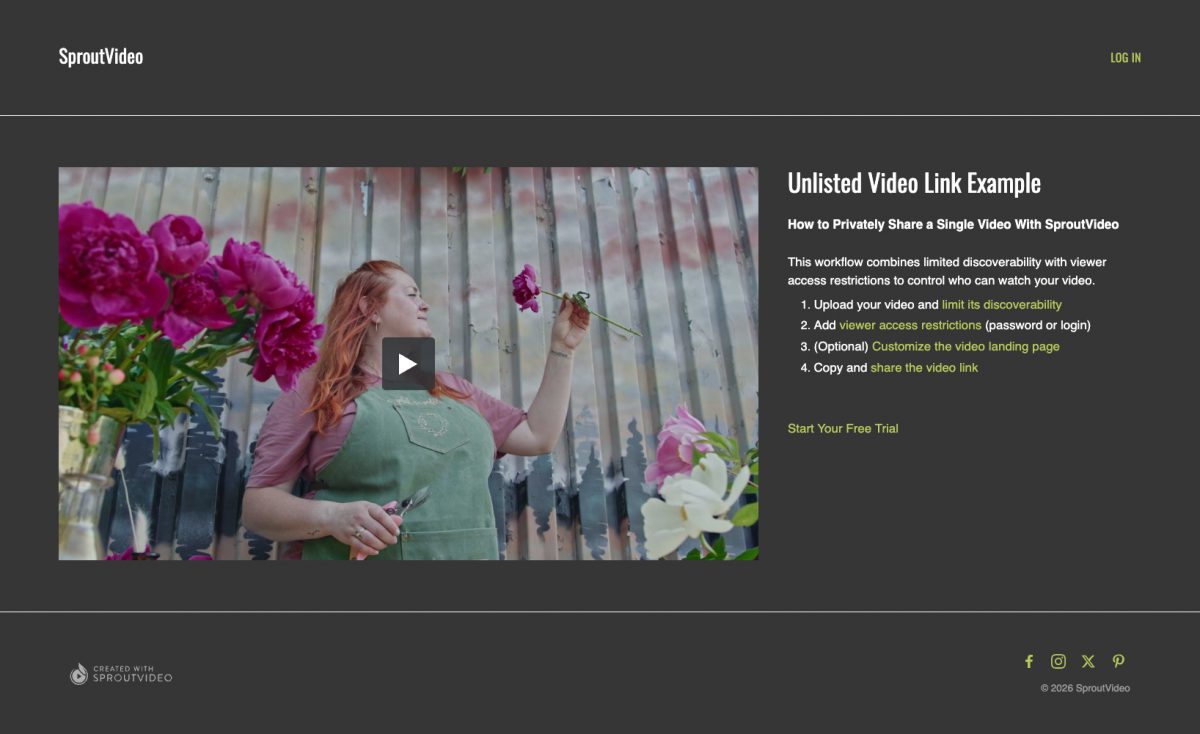
Try It Out! Unlisted Video Link Example
Share a single video with a link. Often referred to as a “private video link,” this unlisted video:
- Is not publicly visible (unless embedded elsewhere)
- Does not allow direct download
- Is blocked from search engine indexing
On its own, this approach does not restrict who can watch unless access controls are added—it only limits where a video can be viewed (the video landing page). If the link is shared, anyone with the link can view the video unless viewer restrictions are applied. For this reason, video links work best for intentional sharing in small, trusted groups.
With SproutVideo, you can add password or login protection on top of a video link. This workflow keeps sharing low-friction while adding control over who can watch.
For example, an advertising agency shares a video draft with a client using a private link so the video isn’t publicly visible or searchable. The client can review the draft immediately, while the agency can see when the video is watched.
2. Protect Videos with A Password
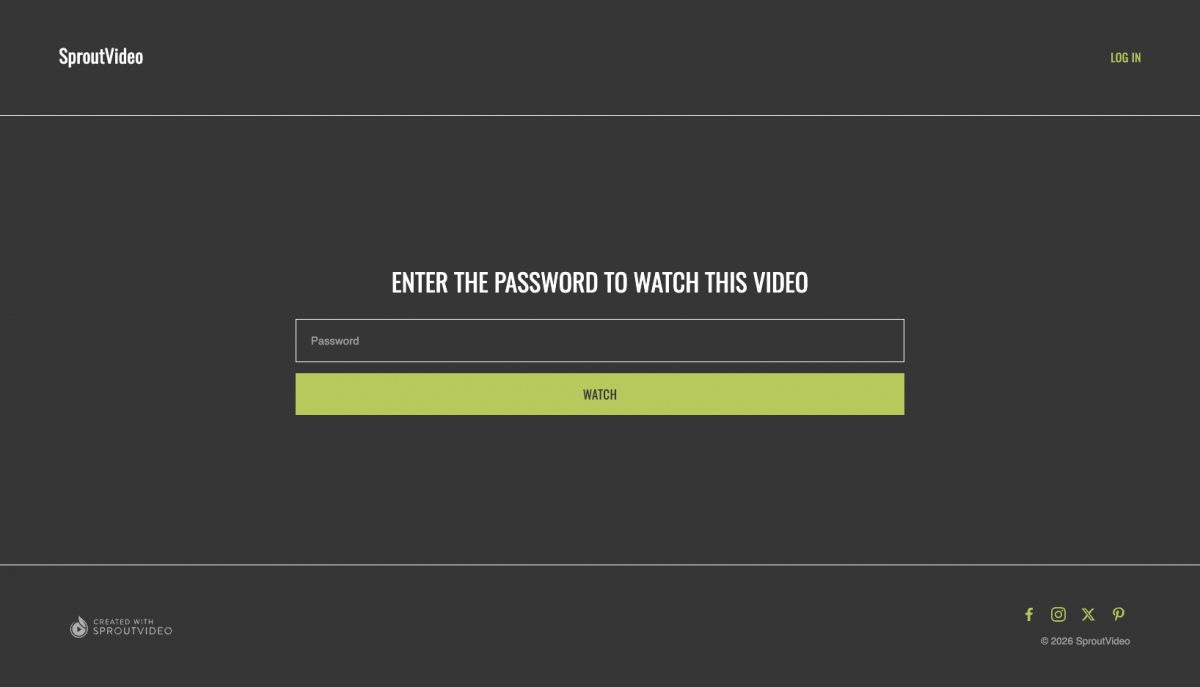
Try It Out! Click and enter password “SproutVideo” to watch.
Quickly share a private video by requiring viewers to enter a password before the video can play. Password protection is a frictionless way to provide temporary or informal video access within a small, trusted group—it does not support user-specific access controls.
You can share password-protected videos on your website, inside an internal portal, or via a private link. Even if someone stumbles upon the video page, they won’t be able to watch it without the password.
Passwords are quick to set up but offer the most basic level of access control, since viewers can still share the password itself freely. If you need to identify individual viewers or revoke access on a per-user basis, see login protection or SSO below.
For example, a parks and recreation department hosts an annual festival and publishes a project hub on its public website. The hub includes password-protected videos with important information for artists and vendors. After participants pay their booth fees, they receive an email with the password and a link to the public page.
Watch or Read: Password-Protected Content and How You Can Use It
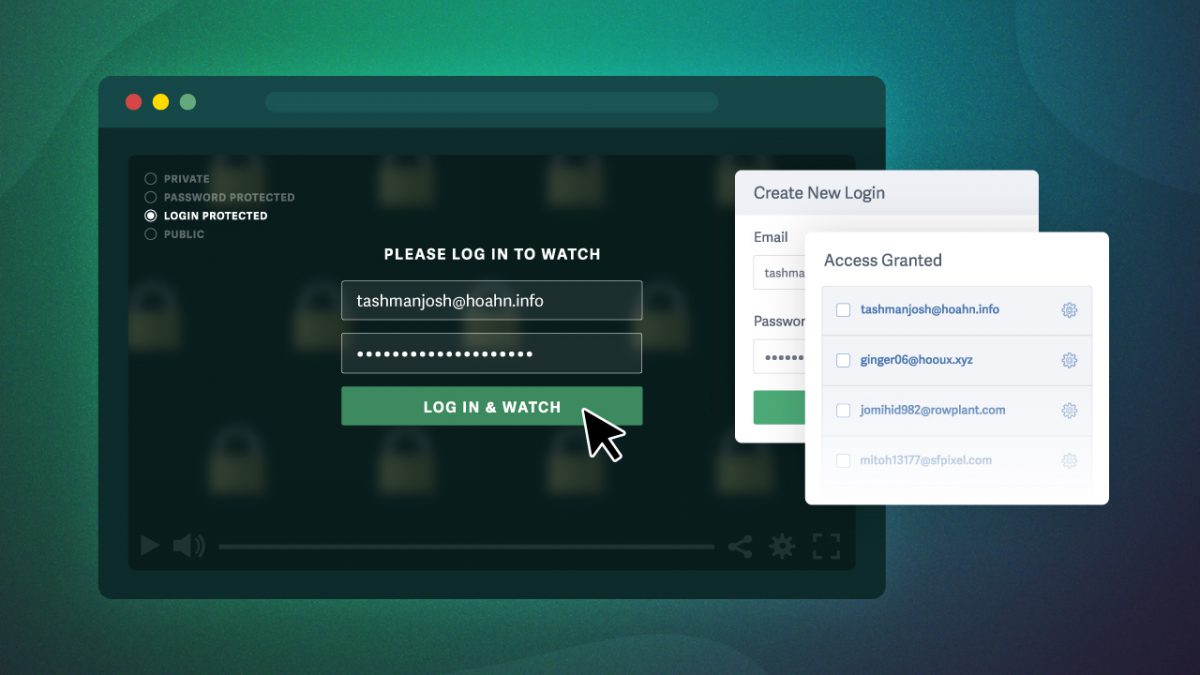
3. Restrict Access with Login Protection (Members Only)
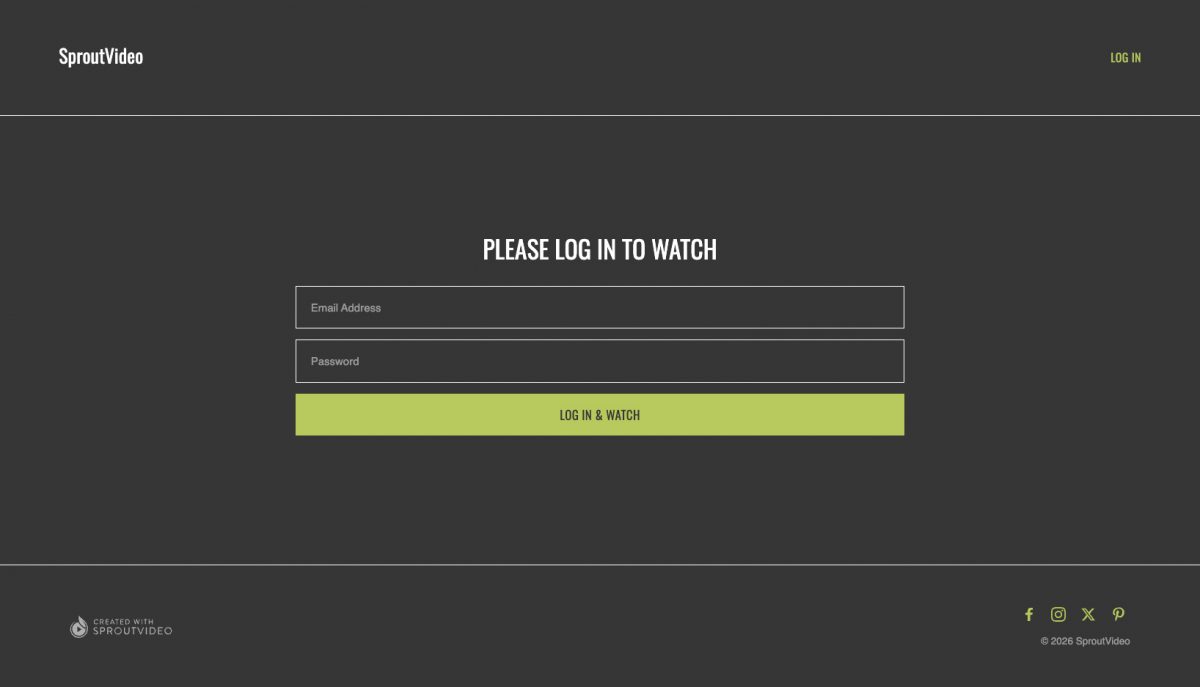
Try It Out! Enter email address “login@protection.com” and password “SproutVideo” to watch.
Control and track video access and engagement at the viewer level, while maintaining an audit trail of viewer activity. Login protection is a self-serve, identity-based access system that requires viewers to sign in with individual credentials.
This option is ideal for employee training, monetized or members-only video content, and other business workflows that require ongoing, user-level access control.
Login-protected videos are delivered through SproutVideo-hosted video websites, which provide a secure viewing environment for authenticated users. Login protection provides precise controls over viewer-level access, including the ability to:
- Decide which videos a viewer can access
- Set how long access lasts
- Limit the number of login sessions per viewer
- Revoke individual access at any time
- Control what content each viewer sees
For example, a fitness influencer sells multiple video courses via their social media link-in-bio page. When a customer purchases a course, they automatically receive login credentials by email. Once logged in, the customer can view and access only the videos they bought.
Get Started: How To Use Login Protection To Control and Monitor Video Access
4. Authenticate Employees with Single Sign-On (SSO)
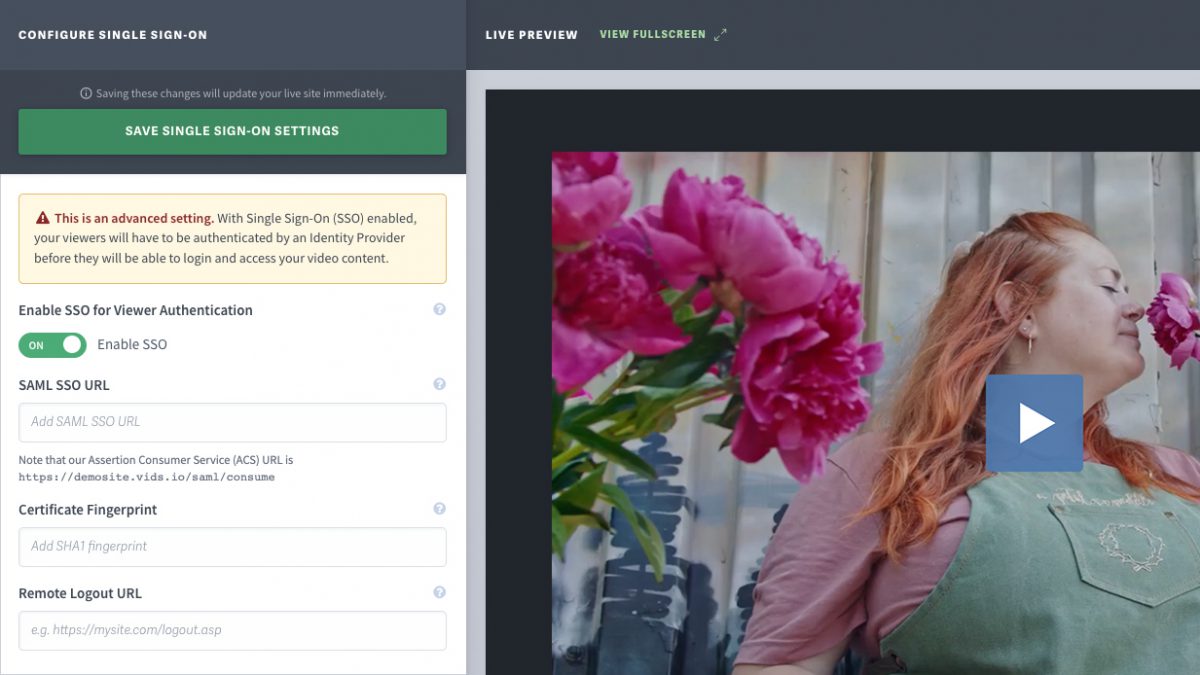
Restrict video access through your company’s existing identity provider with Single Sign-On (SSO). This approach lets employees sign in with the same credentials they already use for other internal tools, providing secure authentication at scale.
SSO is ideal for organizations with centralized identity systems and the technical expertise to support secure, employee-based access across applications. This makes SSO well-suited for corporate training, compliance requirements, leadership communications, and similar workflows.
Similar to login protection, SSO-protected videos are delivered through SproutVideo-hosted video websites to ensure the secure viewing environment needed for identity-based verification.
For example, a global company uses SSO to deliver compliance training videos to employees. Employees sign in with their corporate credentials to access training, and video completion is tied to their verified employee identity to support audits and regulatory reporting.
Enable SSO: How To Require User Authentication with Your Identity Provider
5. Capture Leads with Gated Video Access
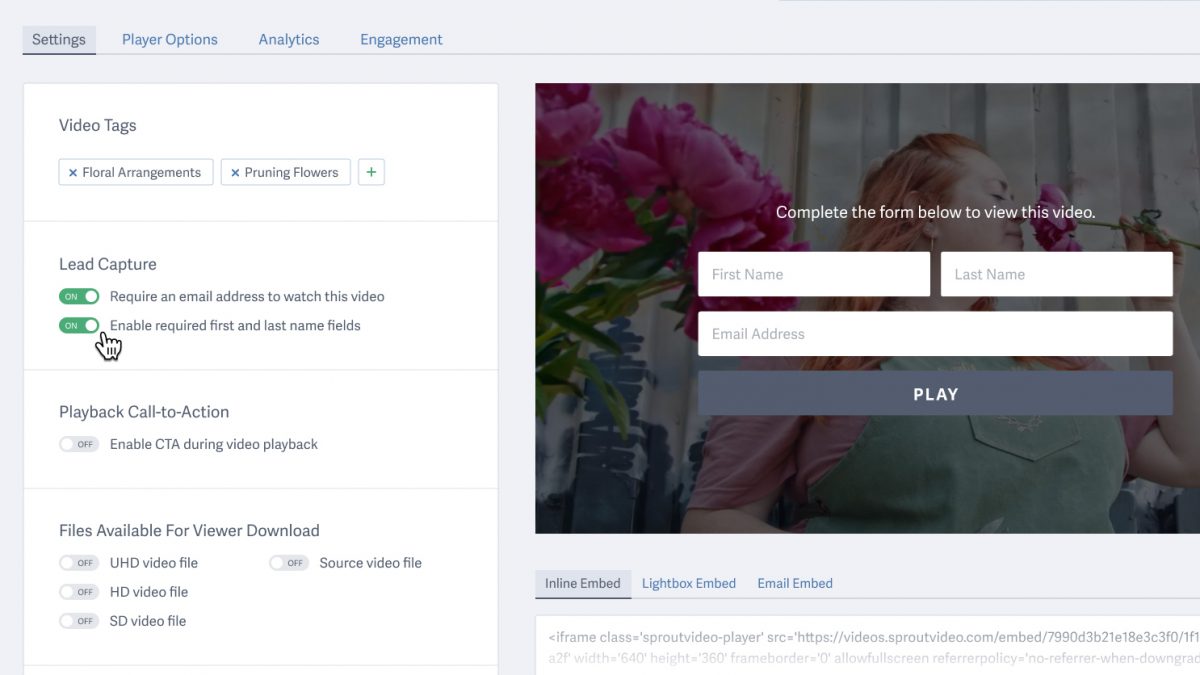
Require viewers to submit their contact information to access a video with lead-capture gating. Businesses use video lead capture for marketing or promotional purposes, but it does not restrict who can watch the video or where they can view it. Instead, viewers can unlock the video with their information, gaining access while enabling the business to follow up.
Lead capture forms can be added to any video, making it easy to collect viewer information on landing pages, blog posts, and anywhere video can be embedded. Gated video access is ideal for product demos, webinars, and any content where lead generation is the primary goal. However, lead capture does not guarantee that viewers will provide accurate information.
For example, a marketing team promotes an on-demand webinar using a gated video. Visitors submit their email address to watch the recording, allowing the team to follow up with attendees while keeping the video inaccessible to casual site visitors.
Pro tip: Want to offer value before gating a video? Use a playlist with an ungated video first, followed by a gated video.
Gate Videos: Use Lead Capture to Require User Contact Information to Watch Your Videos
6. Restrict Video Playback by Region with Geo-Whitelisting
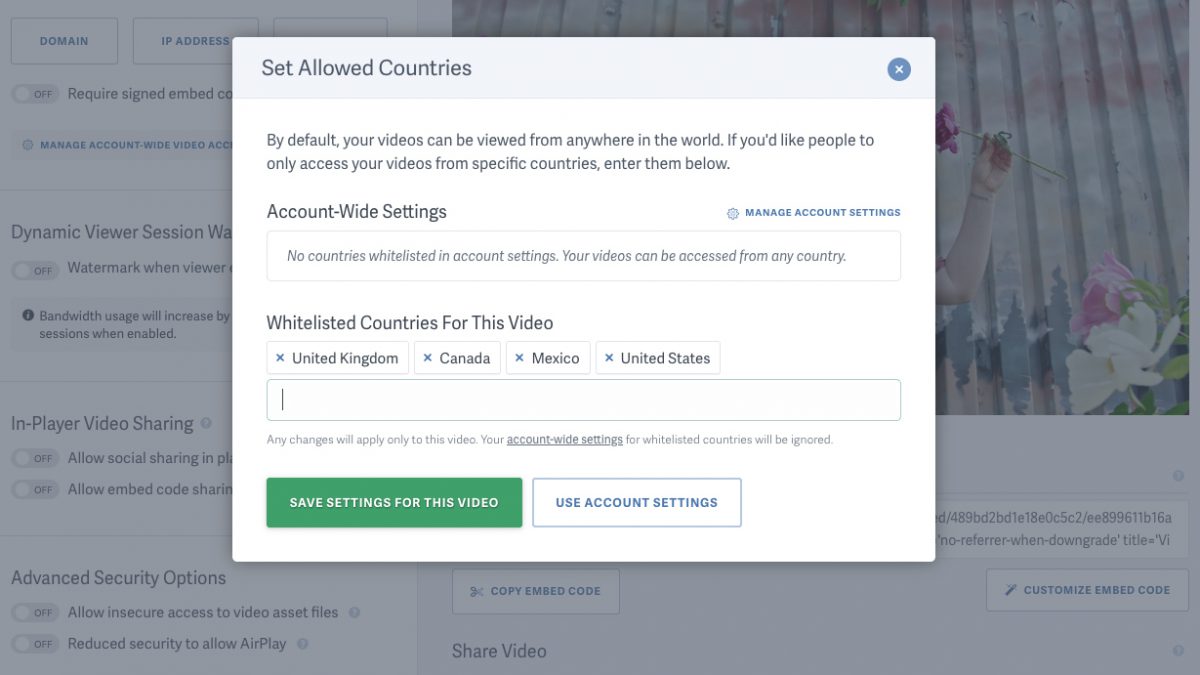
Restrict video access to specific countries or regions with geo-whitelisting. Geo-whitelisting is more secure than geo-blocking, which allows playback everywhere except restricted countries. Instead, geo-whitelisting limits playback to a list of approved countries or regions.
Companies use geo-whitelisting for licensing and distribution, regulatory compliance, and other situations where video content is intended for a specific geographic audience.
For example, a media company licenses a video series for distribution in specific countries. The videos are geo-whitelisted, so they play only in approved regions, ensuring the content is accessible where the company holds rights and unavailable where it does not.
See How: Designate Specific Countries or Regions Where Your Videos Can Be Played
7. Limit Access To Network Connections with IP Restrictions
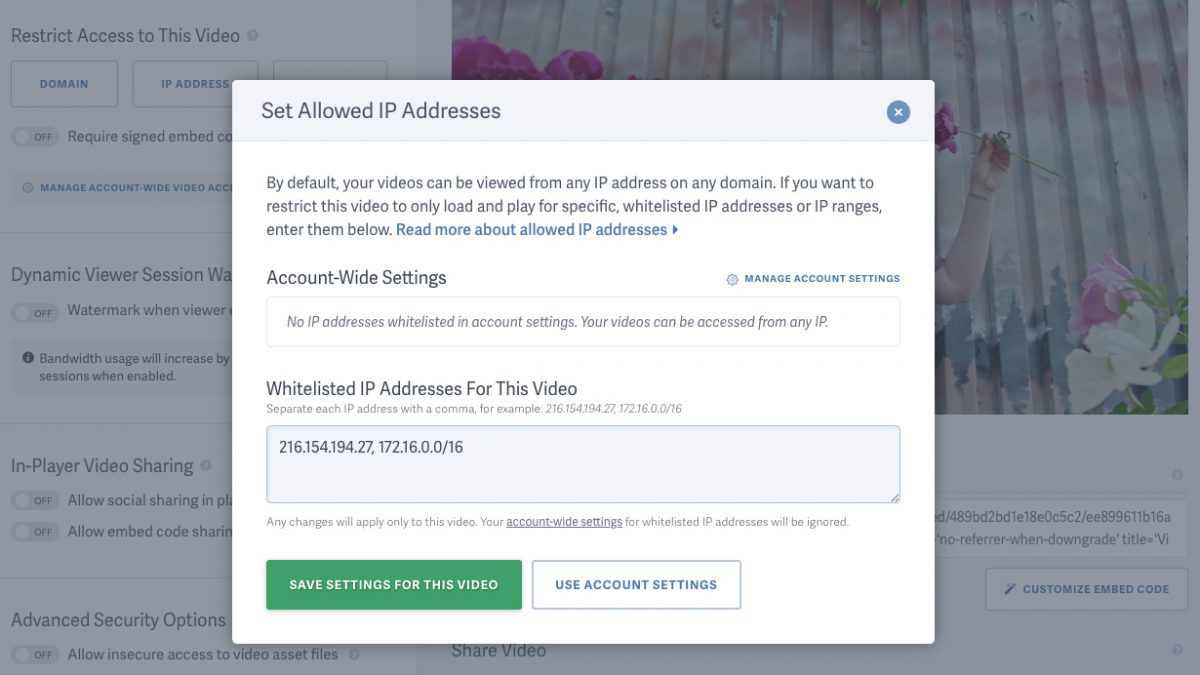
Limit video playback to specific networks with IP address restrictions. Allowed IP addresses restrict viewership to particular network connections. This approach limits playback to specific locations, such as an office, university campus, or financial institution.
Allowed IP addresses are ideal for compliance training, sensitive company communications, and any content that must remain within a controlled environment.
For example, a manufacturing company restricts safety training videos to its corporate offices and factory floors. The company allows videos to play only when accessed from its approved IP address ranges, ensuring employees complete training on-site where the procedures apply.
Learn More: Limit Videos to People Within A Specific IP Address or IP Address Range
Beyond Access Controls: How To Secure & Protect Videos At Every Vulnerability Point
Once someone has access to a video, how do you continue to protect the content?
For businesses, the best practice is to combine restricted video access with theft deterrents (such as dynamic watermarks) and regular security audits to monitor for breaches.
SproutVideo recommends a three-pronged approach for secure and private video sharing:
- Control Video Access: Ensure only permitted viewers can watch content.
- Prevent Leaks and Theft: Keep content safe from unauthorized redistribution.
- Audit Your Security: Regularly monitor access with engagement data.
Learn how to protect your business videos with ease: Read or watch our quick-start guide.