Secure video sharing protects sensitive and internal business communications by preventing unauthorized access, downloading, and distribution.
After all, video is central to how modern businesses communicate. Enterprises share confidential analytics internally. Online course creators protect valuable content. Marketing agencies collaborate with clients. Dispersed teams deliver financial updates to investors.
An unauthorized view, copy, or download exposes businesses to financial loss and legal liability.
Secure video sharing helps businesses confidently distribute confidential videos via a secure video hosting platform designed to protect their content. You can keep your videos safe while collaborating efficiently with secure video features, such as password or login protection, signed embed codes, and dynamic watermarks.
In this complete guide to secure video sharing, you’ll learn:
Table of Contents
- What Is Secure Video Sharing?
- Why Businesses Use Secure Video Sharing
- What Businesses Risk Without Secure Video Sharing
- 5 Questions to Ask Before Sharing Business Videos
- How to Share Videos Securely
- Secure Video Hosting Features to Look For
- The Best Secure Video Hosting Platform
- FAQs on Secure Video Sharing
What Is Secure Video Sharing?
Secure video sharing is the controlled distribution of private video content that protects against unauthorized access, downloads, theft, and leaks. It allows businesses to control who, when, and where viewers can watch a video, using a secure video hosting platform.
Unlike private links and public platforms, secure video sharing protects video assets even after they’re shared by enforcing playback restrictions and maintaining visibility into who watches.
Why Businesses Use Secure Video Sharing
Unauthorized access and distribution of content create real problems for businesses of all sizes and across industries. One leaked video can impact a company’s bottom line, damage brand trust, and expose it to legal liability.
Secure video sharing minimizes risk by providing granular controls that limit viewership to specific teams, locations, networks, and employees.
Common business use cases include:
- Employee Training Videos: Protect operational processes and track compliance.
- Internal Communications: Ensure only authorized staff access sensitive content.
- Confidential Product Demos: Safeguard intellectual property during collaboration.
- Investor Updates: Keep financial information confidential and traceable.
- Client Collaboration: Share private videos safely throughout project workflows.
- Marketing Content Review: Prevent leaks and premature campaign exposure.
In short, secure video sharing protects critical business assets.
What Businesses Risk Without Secure Video Sharing
Even with good intentions, business videos can leak when they aren’t sufficiently protected. Learn more about the ways private video falls into the wrong hands and why each matters.

Forwarded Private Links
Private video links provide quick, frictionless sharing but leave content open to unintended viewers, who can freely share the video link and password.
For example, a real estate agent shares a password-protected walkthrough video with a buyer. The buyer forwards the link and password to an unqualified contact. Strangers view the video, and the seller pulls the listing. Worse still, the agent has no way to trace who leaked it.
Why it matters: Forwarded links can expose sensitive content to unintended viewers.
Video Download Theft
Video downloads are the easiest way for people to gain access to your source video file, allowing them to make copies and redistribute it without a trace. For this reason, preventing video downloads is a top priority for many businesses with private content.
For example, a brand shares an unreleased campaign video with agency partners via a standard cloud link. One partner downloads it, and it’s leaked on social media within hours. The premature reveal kills planned press coverage, forces a last-minute creative pivot, and collapses a media partnership the team spent months building.
Why it matters: Downloaded videos can be copied and redistributed without control.
Accidental Public Indexing
Accidental public indexing is when a video becomes discoverable on search engines. This occurs when a video’s privacy settings are misconfigured on your video hosting platform. An otherwise private video can rank and attract unwanted viewers who find it through search.
For example, a new learning and development manager misconfigures the privacy settings on an internal process video, inadvertently allowing search indexing. Within days, it surfaces in Google search results, making proprietary information and internal processes publicly available.
Why it matters: Unintended viewers can publicly discover videos with misconfigured settings.
Unauthenticated Viewer Access
Individual viewer authentication enables businesses to connect video views to specific viewers, allowing them to track who watches what videos, from where, and how much. This engagement data is essential for creating a trail for security audits and maintaining compliance records.
For example, an HR team distributes mandatory compliance training videos via a company-wide email with an unlisted video link. During an audit, the team must verify which employees completed the training. But HR did not require individual authentication. Therefore, there’s no record of who watched, and they can’t demonstrate compliance.
Why it matters: Without viewer authentication, businesses cannot verify compliance, trace content theft, or monitor potential security leaks.
Screen Recording or Capture
Screen recording is another way viewers can copy and redistribute video content, even when protected with access restrictions. Viewers record the video using their mobile device or a media player software with recording capabilities. Businesses can use visible and invisible watermarks to deter and trace content theft.
For example, a fitness instructor sells access to weekly training videos through a private membership portal. A subscriber screen records several sessions and posts them to a free YouTube channel. Without watermarking, the instructor has no way to identify which subscriber made the recordings or pursue a takedown tied to the source.
Why it matters: Screen recordings of content can be redistributed without your control.
Embed Code Scraping
Embed codes are visible in a webpage’s source code, which means someone can attempt to copy and re-embed a video on another site. Without domain restrictions or playback authentication, the copied embed code can play outside its intended environment.
For example, a company embeds a sensitive internal communications video on a protected intranet page. An employee copying content for a presentation pastes the embed code into a public webpage. Without domain restrictions in place, the video can play outside the company’s intranet, allowing unintended viewers to access internal content.
Why it matters: Without playback restrictions, stolen embed codes can play videos outside their intended environment.
5 Questions to Ask Before Sharing Business Videos
Before you share business videos, use these questions to consider the risks and level of security needed for each piece of content.
- How sensitive is the video content? What is the business impact if the video is leaked or viewed by the wrong people? The more confidential the information, the stronger the protections you’ll need to safeguard your business.
- How will you share your videos? Will videos live on your website, intranet, secure portal, or a third-party platform? Do you need access controls and ways to protect content even after viewers access it?
- Who should be able to view the videos? Identify the intended audience: teams, departments, clients, or investors. Limiting viewership reduces the risk of accidental leaks and makes monitoring viewers easier.
- Where can viewers access the videos? Decide whether viewers need mobile access, off-network access, or if access should be restricted to specific locations or IP ranges.
- How important is seamless access versus strict security? Decide whether ease of viewing tight security is the priority. Should viewers be able to watch without friction, or is secure sharing important even if it adds extra steps?
Your answers to these questions will guide which secure video sharing features and workflows you need to protect your business, ensuring content remains private, controlled, and trackable.
How to Share Videos Securely
The Three Pillars of Secure Video Sharing
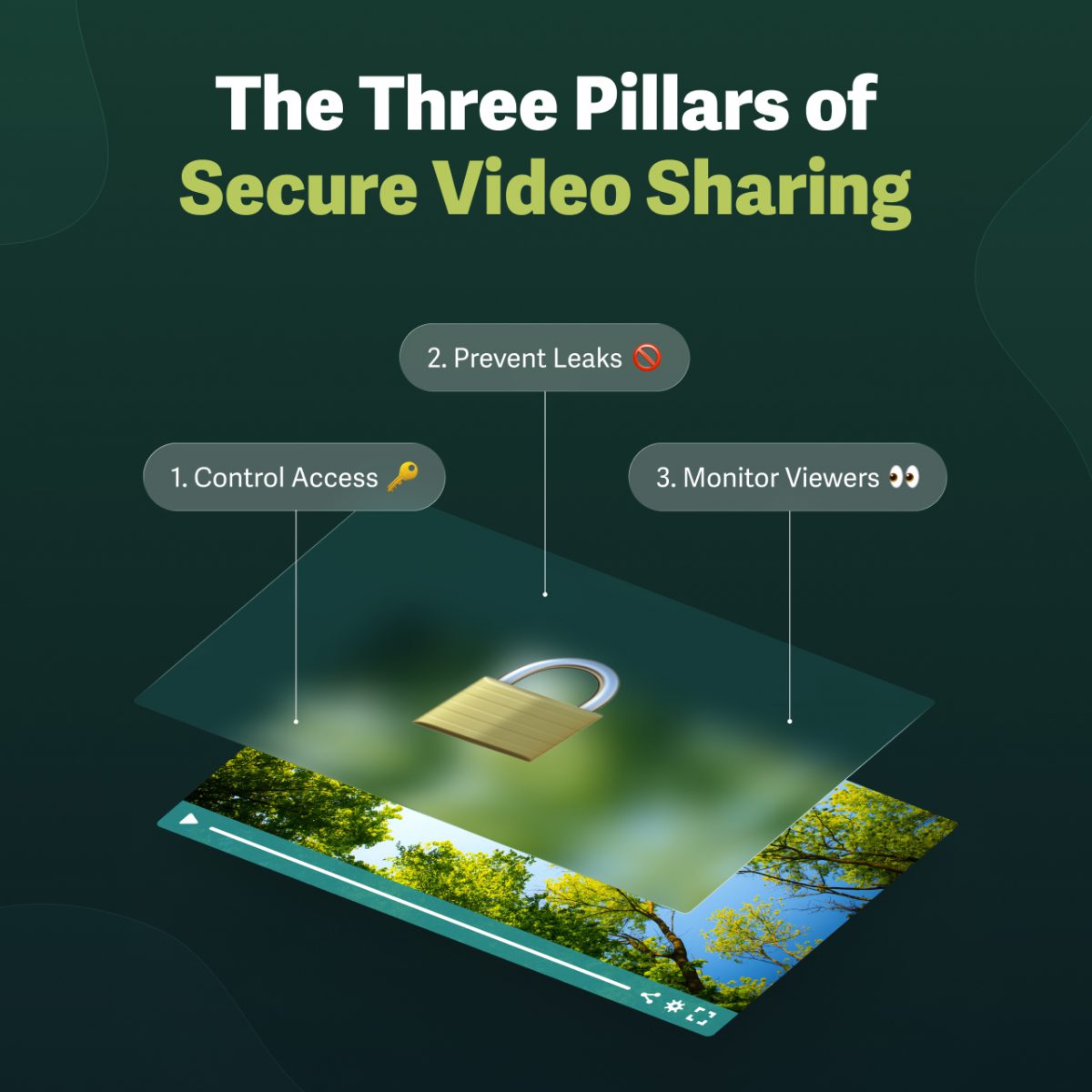
To keep videos safe, consider all potential access points and leaks. Build your secure video sharing strategy around three pillars:
- Control Video Access: Restrict who can watch your videos and protect your account.
- Prevent Leaks and Theft: Stop unauthorized copying, downloading, and distribution.
- Monitor Viewers & Account: Audit engagement data and viewer logs regularly.
For example, a global company uploads a training video for new employees:
- Control Video Access: Each new hire must log in to watch. The video is also restricted to the company’s IP network, ensuring viewers can access it only on authorized devices.
- Prevent Leaks & Theft: A dynamic watermark displays the viewer’s name and email address, moving across the screen to prevent removal.
- Monitor Viewers & Account: Managers review access logs and engagement metrics to confirm the hire completed the training.
Together, these measures ensure videos remain private, secure, and monitorable.
| Control Video Access | Passwords, Login protection, IP/geographic restrictions, SSO | Forwarded links, Unauthenticated viewer access, Access from unapproved locations |
| Prevent Leaks & Theft | Signed embed codes, Download prevention, Dynamic watermarks | Stolen embed codes, Downloaded videos, Untraceable screen recordings |
| Monitor Viewers & Account | Viewer access logs, Engagement analytics, Account audit logs | Compliance gaps, Untraceable viewers, Security leaks |
7 Steps to Share Videos Securely
Build a secure video sharing workflow for your business. Follow these seven steps to protect sensitive content, reduce risk, and ensure only the right people can access your videos.
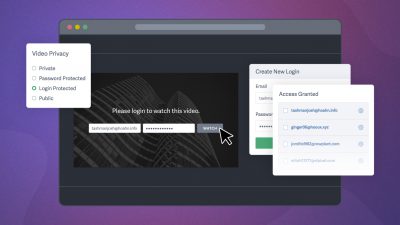
1. Restrict Video Access by Viewer
Limit who can watch videos with password protection or credential-based access (login protection). Businesses can also use SSO to limit viewership while streamlining credentials across tools by connecting to their chosen identity provider.
If your current video portal includes access controls, you can use embed code or URL tagging to pass viewer information to your engagement metrics dashboard.
When it’s needed: Anytime you need to restrict viewership to a specific audience (employees, teams, or clients) and track individual engagement.
Example: A marketing agency shares confidential strategy videos with its creative team. Each team member must log in with their company credentials to watch, preventing outside contractors from accessing sensitive plans while the agency tracks individual engagement.
Need a dedicated, secure video portal? Create one in minutes
2. Restrict Video Access by Location or Network
Limit who can watch videos based on where they’re accessing them from, such as specific countries or approved office locations. Use IP address or geographic location restrictions to prevent views from outside approved physical and online locations.
When it’s needed: Anytime you need viewers to access content only from specific geographic locations and IP networks.
Example: A streaming service distributes video content with international partners, but the license allows viewing only in certain countries. The platform restricts access by geographic location, so only viewers in authorized regions can watch.
Tip: Combine with password or login protection for layered security, ensuring videos are only viewable by the right people, in the right place.
3. Prevent Video Downloads
Once a viewer can access your video, it’s essential to prevent downloads, which can be copied and redistributed without a trace. A secure video hosting platform like SproutVideo prevents content from being downloaded by default. To maintain this protection, always use embed codes rather than direct video links.
When it’s needed: Anytime you share video content that must remain online-only.
Example: An agency shares a work-in-progress with a client. By preventing downloads, the client can view and provide feedback while the agency maintains control of the content.
4. Control Playback with Domain Restrictions
Restrict where your videos can play by approving only specific domains. Allowed Domains checks the URL of the original embed code and blocks playback on unauthorized sites.
When it’s needed: Anytime you want to prevent unauthorized websites from playing content.
Example: A software company embeds product demo videos on its official support site and partner portals. Allowed Domains ensure videos cannot be displayed on unrelated websites or competitors’ pages, protecting intellectual property and brand presentation.
5. Control Playback with Signed Embed Codes
Prevent unauthorized playback of your videos with signed embed codes. Similar to allowed domains, this feature limits where viewers can watch your video.
While domain restrictions control whether a video can load, signed embed codes determine whether a playback request is valid, ensuring the video can play only within its intended environment. This means they control playback even where domain restrictions may not be reliable, such as in a mobile app, behind a login, or within a user-specific session.
When it’s needed: When you need to prevent embed code reuse or unauthorized playback in environments where domain restrictions alone are insufficient.
Example: A fitness platform delivers premium workout videos through its mobile app. Because the content is not tied to a fixed domain, domain restrictions alone cannot prevent misuse. Each time a user plays a video, the platform generates a signed embed code tied to that session. If someone extracts and shares the embed code, it cannot be reused outside the app.
6. Deter Screen Recording & Trace Theft
Protect your videos from unauthorized copying with dynamic watermarking, which deters screen recording and identifies content theft. There are two types of dynamic watermarks:
- Visible Watermarks: Burned-in watermarks display the viewer’s email, IP address, and session ID. They move across the screen, making them difficult to remove or crop out.
- Invisible Watermarks: Hidden from the viewer, these marks allow our team to trace unauthorized copies back to the source.
You can customize visible watermarks by adjusting opacity, timing, and placement to avoid covering center-focused content.
When it’s needed: Anytime you share premium or confidential video content where you need to deter theft and/or trace unauthorized copies.
Example: A piano instructor streams weekly videos to paying members. If a video is screen-recorded and shared online, dynamic watermarks let the instructor trace it to the subscriber who accessed it and remove them from the group, protecting their business.
Learn More: What Are Dynamic Watermarks for Videos?
7. Monitor Viewers & Account Activity
Regularly review who is accessing your videos to ensure security measures are working and content remains protected.
- Engagement Metrics: Look for unusual email addresses, locations, IP addresses, or viewing patterns. If anything seems suspicious, temporarily revoke access, adjust privacy settings, or remove the video from the page.
- Viewer Access Log: Track individual viewer engagement, including who accessed which videos and how long they watched each.
- Account Audit Log: Monitor team members with direct access to the video hosting account: see who uploaded videos, changed privacy settings, or edited account details.
When it’s needed: Anytime you need to verify compliance or monitor for security breaches.
Example: A corporate HR team distributes mandatory compliance training videos. By reviewing viewer logs and engagement metrics, managers can confirm that all employees have completed the training and spot any unusual activity, helping maintain compliance and secure access.
Secure Video Hosting Features to Look For
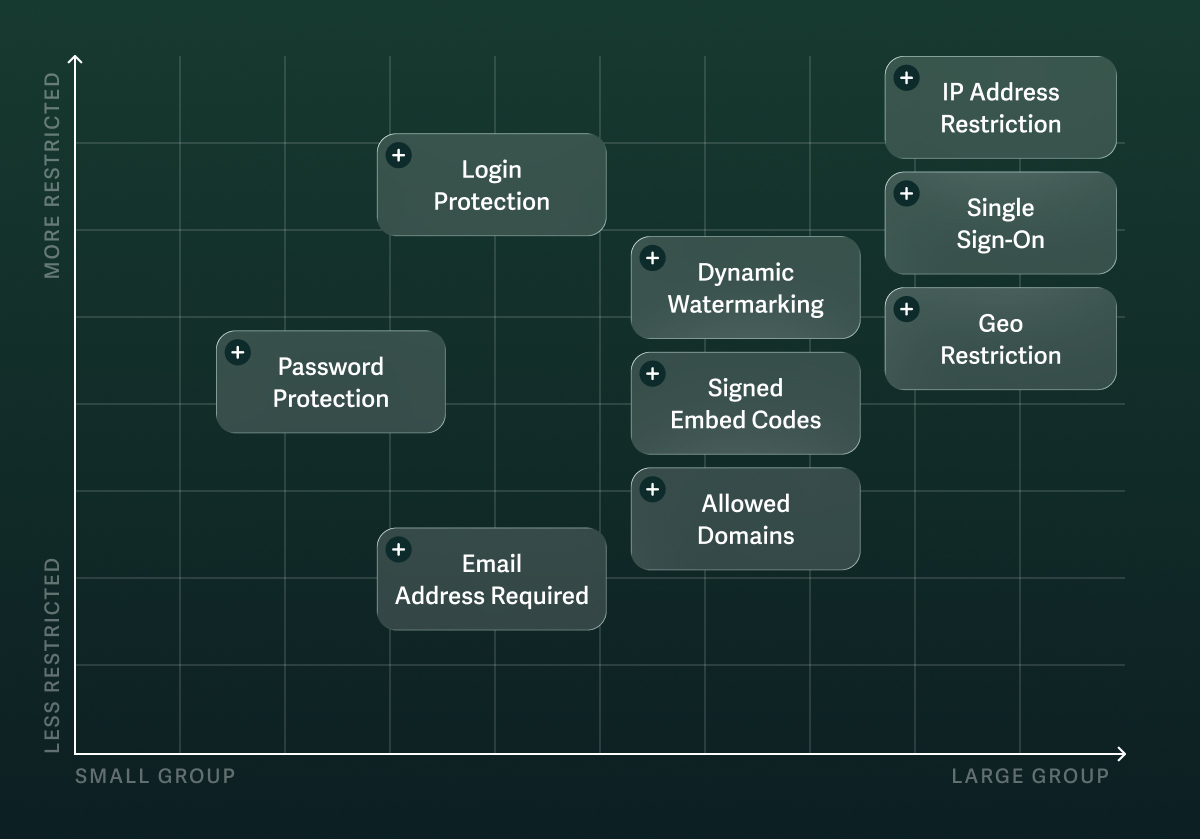
Not every video requires the same level of protection. Use this list to identify the features that underpin your secure video hosting workflow, grouped by secure video-sharing pillar.
Control Access
- Password-Protected Video: Require a password to access video content.
- Login-Protected Video Access: Create login credentials that are required to view videos.
- Single Sign-On (SSO): User authentication with one set of credentials. Connect your hosted video website platform (e.g., SproutVideo) to your Identity Provider.
- IP and Geographic Restrictions: Control what IP addresses and geographic regions can access your content.
Deter Theft & Prevent Leaks
- Download Prevention: Prevent users from saving local copies of videos.
- Domain Restrictions: Control what domains can load and play your content.
- Signed Embed Codes: Control playback and prevent unauthorized reuse.
- Dynamic Video Watermarks: Display the viewer’s email address, IP address, and session ID on the video to deter theft and trace unauthorized copies.
Monitor Viewers & Account
- Engagement Metrics: Track how viewers interact with your videos using heat maps and session data to monitor engagement and improve performance.
- Viewer Access Log: Track individual viewer engagement to see who is watching, how long they watch, and detect unusual patterns that could indicate security issues.
- Account Audit Log: Review team members’ changes to videos and privacy settings.
All of these features (and more) are available through the SproutVideo platform.
The Best Secure Video Hosting Platform
Secure online video hosting platforms aren’t one-size-fits-all. Evaluate your business needs to choose the platform that best fits your video business requirements.
One option? SproutVideo is secure video hosting for businesses of all sizes. With a dedicated support team and an intuitive platform, your company gains complete control over video content with enterprise-grade security and engagement tracking—without ads and unwanted branding.
See the platform in action with our 2-minute walkthrough video:
Ready to get started? How To Secure & Protect Videos with SproutVideo
FAQs on Secure Video Sharing
How do I share a video securely?
The safest, most secure way to share a video is to control who can watch and revoke access if something looks off.
This control is enabled by restricting viewer access, limiting where content can play, and monitoring engagement patterns that might signal it has reached the wrong hands. For additional security, deter unauthorized recording by making any redistributed copies traceable to their source. A private video hosting platform provides the necessary layered security.
How do I share a password-protected video?
Password protection allows you to share videos quickly and with low friction while keeping access limited to your intended audience. Simply set a password on your video and share the link to its page.
For confidential content, consider alternative access controls (such as login protection) or combine password protection with additional security measures, since viewers can easily share passwords.
On the SproutVideo platform, users can share password-protected videos via a link, an embedded video on a website or other portal, or a SproutVideo-hosted video website.
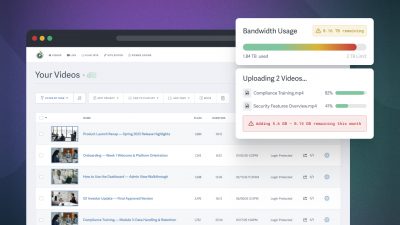
How do I share large private videos?
Send large private videos with a secure video hosting platform following these steps:
- Upload the video to the platform
- Choose your access controls
- Share it via an embedded player or protected link
This workflow keeps the video online-only and allows you to limit who can watch, prevent direct downloads, and monitor engagement.
How do I share a video with a set access duration (expiration date)?
An expiration date limits access to a set timeframe, preventing viewers from opening the video even if they still have the link.
Video hosting platforms provide multiple ways to control video expiration, such as time-limited links, expiring login credentials, and session-based tokens that automatically revoke access.
The SproutVideo platform uses login protection to provide session- and time-limited access. When granting login access to viewers, you can specify the start and end dates and times, as well as the number of sessions permitted before video access expires.
How do I prevent videos from being downloaded?
To allow viewers to stream your content while preventing downloads:
- Use a video hosting platform that blocks direct downloads.
- Avoid sharing direct file access, as it can lead to unintentional downloads.
- Protect videos by using embed codes or secure video pages instead of direct file links, which expose the video file itself and make downloading possible.
Can I track who watches my videos?
Yes! Engagement metrics provide viewer information about each viewing session, including time, IP address, location, and device. You can also track individual viewers using login protection or viewer tagging, which ties video sessions to specific users in your metrics.